API Security • Penetration Testing • Application Security
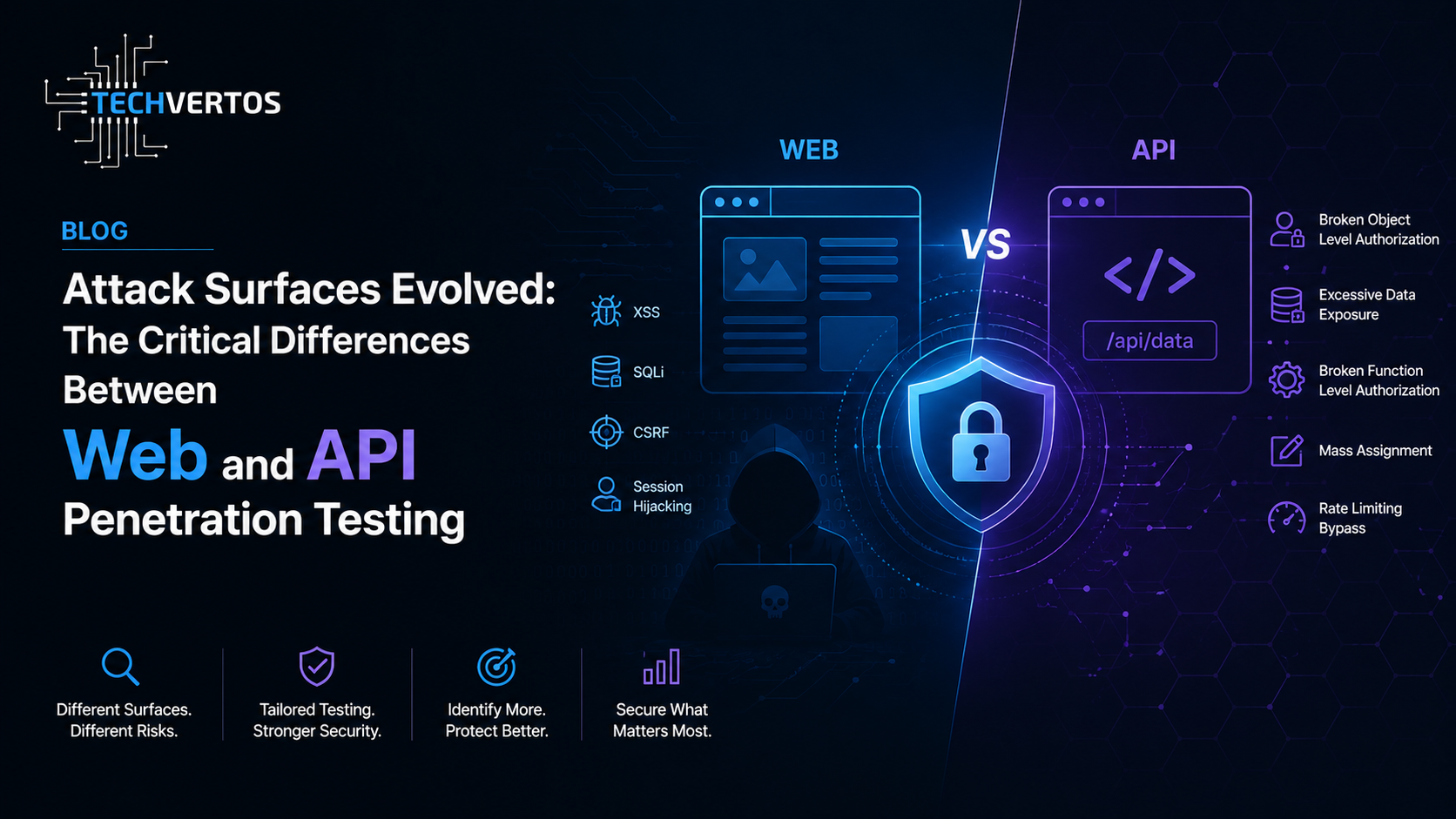
Attack Surfaces Evolved: The Critical Differences Between Web and API Penetration Testing
Modern applications no longer live inside a single web server rendering HTML pages. Today’s systems operate through interconnected APIs powering mobile apps, SaaS platforms, cloud-native microservices, and AI-driven applications. As architecture evolved, the attack surface quietly multiplied.
The Evolution of Modern Applications
Traditional web applications were mostly monolithic. The backend handled:
- User authentication
- Business logic
- Database queries
- HTML rendering
- Session management
Security testing mainly focused on the browser-facing UI layer. Penetration testers searched for vulnerabilities such as:
| Traditional Web Vulnerability | Impact | Example |
|---|---|---|
| Cross-Site Scripting (XSS) | Session hijacking | Injecting JavaScript into comments |
| Cross-Site Request Forgery (CSRF) | Unauthorized actions | Forced password change request |
| Clickjacking | UI deception | Invisible malicious iframe overlays |
| SQL Injection | Database compromise | Dumping user credentials |
But modern applications rarely work this way anymore.

The Shift from Monoliths to APIs & Microservices
Modern applications now operate as distributed ecosystems where:
- Frontend applications are lightweight clients
- Mobile apps communicate directly with APIs
- Microservices exchange data internally
- Third-party integrations constantly interact with backend systems
- Cloud-native architectures expose hundreds of endpoints
Instead of one large application, organizations now manage dozens or even hundreds of APIs.
Frontend App
↓
API Gateway
↓
Authentication Service
User Service
Payment Service
Notification Service
Analytics Service
Every API endpoint becomes a potential entry point for attackers.
Why API Penetration Testing is Fundamentally Different
API penetration testing is not simply “web pentesting without a browser.” It requires a completely different methodology, mindset, and attack strategy.
1. The UI Disappears
Traditional web pentesting relies heavily on crawling visible webpages and following links.
APIs have no visible interface.
📌 Example Scenario
A banking mobile application may communicate with:
/api/v2/accounts/api/v2/transactions/api/v2/cards/internal/admin/export
None of these endpoints are publicly visible in a browser.
Attackers often discover them through:
- Intercepting mobile traffic with Burp Suite
- Reverse-engineering APK files
- Inspecting JavaScript source files
- Analyzing Swagger/OpenAPI documentation leaks
Why This Matters
Security scanners cannot test endpoints they cannot discover. Hidden APIs often become forgotten attack surfaces.
2. API Security Focuses More on Business Logic
Traditional web testing focused heavily on injection flaws. APIs still suffer from injection attacks, but modern API breaches are increasingly caused by:
- Broken authorization
- Business logic abuse
- Privilege escalation
- Improper access control
- Weak object ownership validation
Understanding Common API Vulnerabilities
BOLA: Broken Object Level Authorization
BOLA is one of the most dangerous API vulnerabilities today.
📌 Example Scenario
GET /api/orders/1001
A user changes the request manually:
GET /api/orders/1002
If the API returns another customer’s order details, the application suffers from BOLA.
Attackers can access invoices, medical records, banking data, support tickets, or internal documents simply by changing object IDs.
Mass Assignment Vulnerabilities
APIs commonly accept JSON request bodies. Poor backend validation may allow attackers to inject unexpected parameters.
📌 Example Scenario
{
"username": "john",
"email": "john@example.com",
"is_admin": true
}
If the backend blindly trusts user input, attackers may grant themselves administrative privileges.
Improper Asset Management
Many companies leave old API versions active after upgrades.
📌 Example Scenario
/api/v1/auth→ Old vulnerable endpoint/api/v2/auth→ Patched secure endpoint
Attackers intentionally search for outdated API versions because they often lack:
- MFA enforcement
- Rate limiting
- Modern authentication controls
- Security patches
Web Pentesting vs API Pentesting
| Area | Web Pentesting | API Pentesting |
|---|---|---|
| Primary Focus | Frontend/UI vulnerabilities | Backend logic & authorization |
| Discovery Method | Crawling webpages | Traffic interception & documentation |
| Common Risks | XSS, CSRF, Clickjacking | BOLA, Mass Assignment, Auth flaws |
| Testing Tools | DAST scanners | Burp Suite, Postman, API fuzzers |
| Authentication Testing | Sessions & cookies | JWTs, OAuth, API keys |
Methodology Adjustments for Modern Security Teams
Organizations can no longer rely solely on traditional web security assessments.
Effective API security testing requires:
- Swagger/OpenAPI documentation
- Postman collections
- Multiple user-role accounts
- Authentication tokens
- GraphQL schemas
- Access to staging environments
Critical Areas to Test
- Horizontal privilege escalation
- Vertical privilege escalation
- Broken authentication flows
- Rate limiting bypasses
- Sensitive data exposure
- Business logic abuse
The False Sense of Security Problem
Many organizations run automated DAST scanners against frontend applications and assume they are secure.
But modern attacks increasingly bypass the frontend entirely and target APIs directly.
Traditional web pentesting alone is no longer sufficient for modern applications. APIs have become the real operational backbone of digital systems, and securing them requires dedicated API security testing, business logic analysis, and deep authorization validation.